Russia arrests suspected owner of LeakBase cybercrime forum
Russian police arrested a Taganrog resident believed to be the owner of LeakBase, a major online forum used by cybercriminals to buy and sell stolen data and hacking tools.

AI-Generated Summary
Russian police arrested a Taganrog resident suspected of owning and administering LeakBase, a major cybercrime forum with over 142,000 members used for trading stolen data, exploits, and hacking tools. The arrest follows 'Operation Leak' in March 2026, an international law enforcement operation coordinated by Europol involving the FBI and 14 other countries that seized the forum's domain and conducted around 100 enforcement actions worldwide. LeakBase was the successor to RaidForums and BreachForums, continuing a pattern of major cybercrime marketplace takedowns.
Threat Actor
ARES threat group / LeakBase operators
Affected Sectors
Frameworks
Aggregated from BleepingComputer
This article was automatically aggregated from an external source. Content may be summarized.
Full Analysis

Russian police in the Rostov region arrested a Taganrog resident believed to be the owner and administrator of LeakBase, a major online forum used by cybercriminals to buy and sell stolen data and hacking tools.
According to a report from the Russian state-owned news agency TASS, Russian Ministry of Internal Affairs spokesperson Irina Volk, who announced the arrest, said the unnamed suspect is also accused of creating the LeakBase hacker platform.
LeakBase surfaced in 2021 as a project supported by the ARES threat group, gradually growing its user base to over 142,000 members after the Breached hacker forum shut down in March 2023.
The forum was free to join and was used by members to sell stolen databases, data leaks, exploits, and other cybercrime services, and also hosted spaces for programming, hacking tips, social engineering, cryptography, and opsec guides.
In March 2026, the FBI and law enforcement agents in 14 other countries took down the LeakBase cybercrime forum in an international joint operation coordinated by Europol, known as "Operation Leak."
Investigators also executed search warrants, conducted interviews, and made arrests in the United States and across Australia, Belgium, Poland, Portugal, Romania, Spain, and the United Kingdom.
The LeakBase website (leakbase[.]la) now displays a notice warning that "This website has been seized by the Federal Bureau of Investigation (FBI) as part of an international law enforcement operation." The seizure banner also notes that the forum's database and its contents, including private messages and IP logs, will be used as evidence in future investigations.
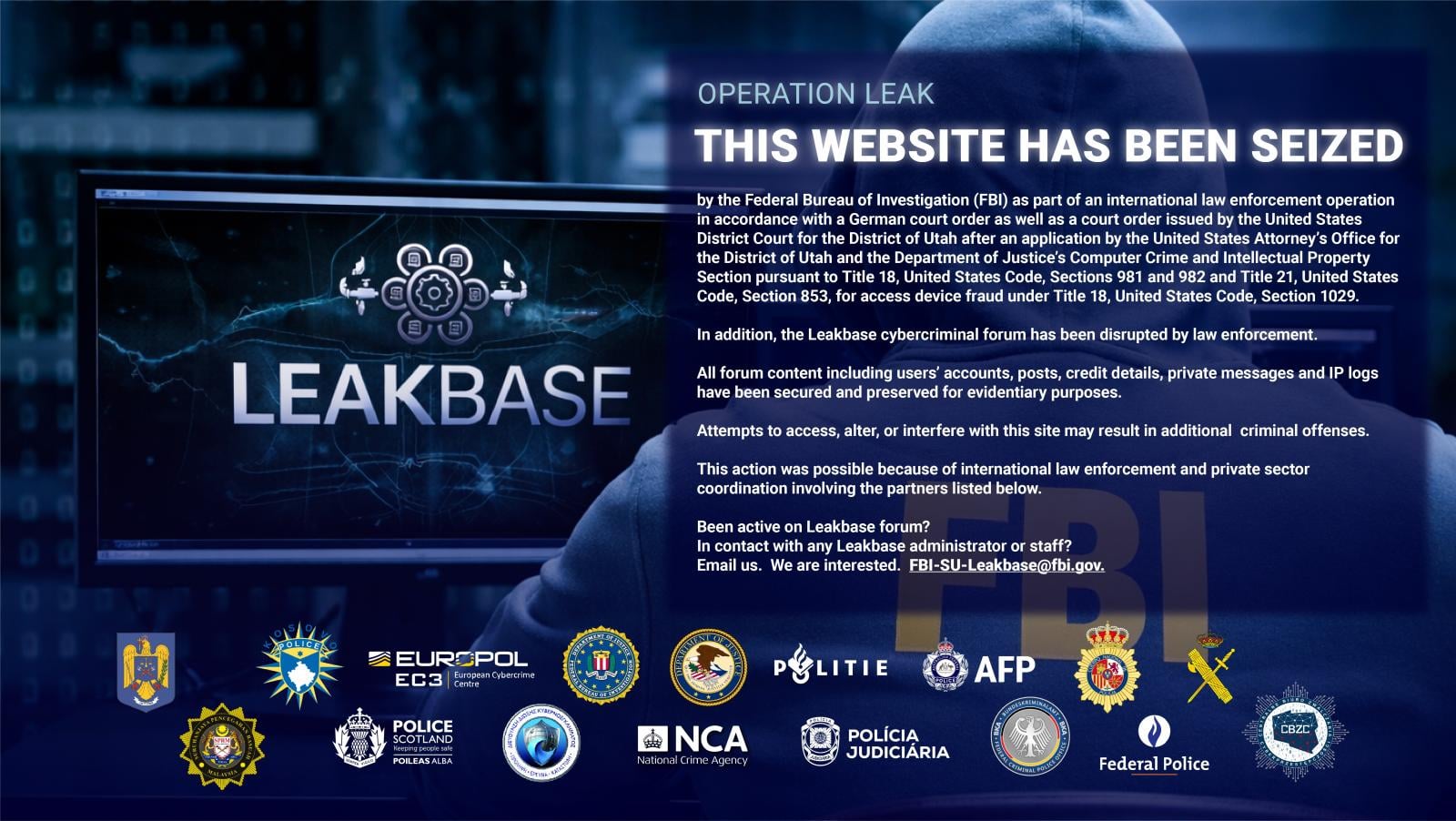
"On 3 March, law enforcement authorities carried out coordinated enforcement actions across multiple jurisdictions, including arrests, house searches, and 'knock-and-talk' interventions. Around 100 enforcement actions were conducted worldwide, including measures against 37 of the most active users of the platforms," Europol said at the time.
"On 4 March, authorities moved to the technical disruption phase, seizing the forum's domain and replacing it with a law enforcement splash page. The operation now enters a prevention phase aimed at deterring further criminal activity and raising awareness of the consequences of engaging in cybercrime."
LeakBase was shut down after law enforcement took down RaidForums in 2022 and BreachForums in 2023, two other major cybercrime marketplaces that preceded it.
Red Report 2026: Why Ransomware Encryption Dropped 38%
Malware is getting smarter. The Red Report 2026 reveals how new threats use math to detect sandboxes and hide in plain sight.
Download our analysis of 1.1 million malicious samples to uncover the top 10 techniques and see if your security stack is blinded.
Originally published by BleepingComputer
Original Source
BleepingComputer