Ransomware Group Takes Credit for Trellix Hack
RansomHouse has published several screenshots to demonstrate access to internal Trellix services.

Aggregated from SecurityWeek
This article was automatically aggregated from an external source. Content may be summarized.
Full Analysis
The RansomHouse ransomware group has taken credit for the recent attack on the cybersecurity firm Trellix.
The Trellix hack came to light this week when the company announced on its website that part of its source code repository had been breached.
“Based on our investigation to date, we have found no evidence that our source code release or distribution process was affected, or that our source code has been exploited,” the company stated.
No other information has been shared by Trellix, but it has promised to release additional details after it completes its investigation.
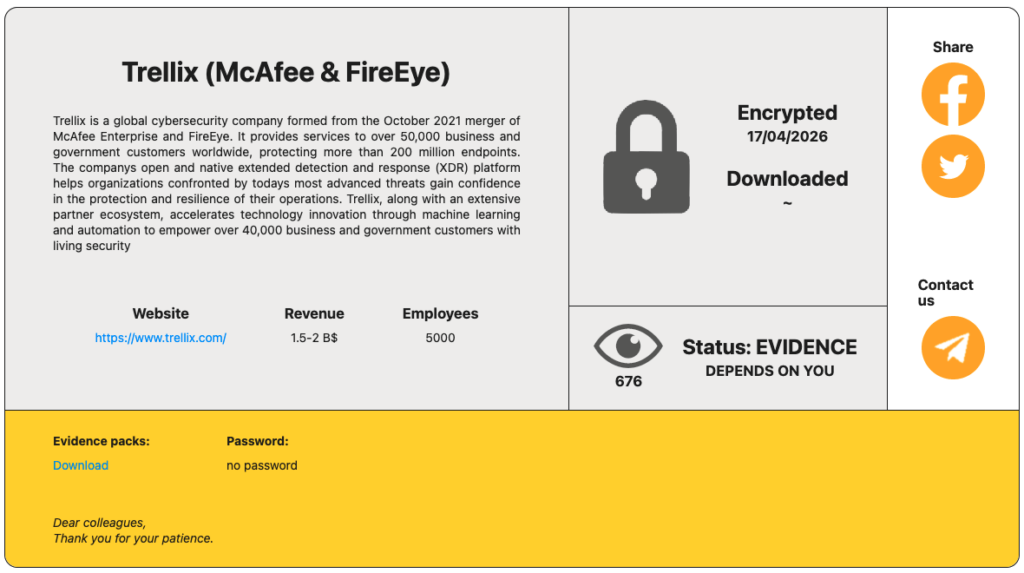
The RansomHouse group named Trellix on its leak website on Thursday. The hackers have not specified how much data they stole from the cybersecurity company, but have published several screenshots that appear to show they had access to internal services and management dashboards.
The hackers have not made any claims regarding the type of data they have stolen from Trellix.
When the incident came to light, SecurityWeek reported that the timing of the attack suggested a potential connection to the recent supply chain attack linked to the hacker groups TeamPCP and Lapsus$. This campaign has impacted several cybersecurity firms, including Checkmarx, Aqua Security, and Bitwarden.
Advertisement. Scroll to continue reading.
The connection has yet to be confirmed, but it’s worth noting that TeamPCP has reportedly partnered with ransomware groups.
SecurityWeek has reached out to Trellix for comment and will update this article if the company responds.
RansomHouse is an extortion group that emerged in 2022, primarily operating as a ransomware-as-a-service (RaaS) provider that targets large enterprises. The group has been known to encrypt victims’ files and steal valuable data to increase its chances of receiving a ransom payment.
RansomHouse’s Tor-based leak website currently lists more than 170 victims.
Related: Vendor Says Daemon Tools Supply Chain Attack Contained
Related: Security Firm Aura Discloses Data Breach Impacting 900,000 Records
Related: Taiwan Security Firm Confirms Flaw Flagged by CISA Likely Exploited by Chinese APTs
Originally published by SecurityWeek
Original Source
SecurityWeek