AI Coding Agents Could Fuel Next Supply Chain Crisis
“TrustFall” attack shows how AI coding agents can be manipulated into launching stealthy supply chain compromises.

Aggregated from SecurityWeek
This article was automatically aggregated from an external source. Content may be summarized.
Full Analysis
Researchers from Adversa.AI have discovered an issue that allows attackers to abuse Claude Code’s automation, potentially creating a new supply chain threat.
Agentic AI is designed to operate automatically and usually invisibly to make our work easier and more efficient. AI code generators are no different. Claude Code (launched in May 2025) has become the fastest-growing tool in the startup and high-end engineering space, with the highest user satisfaction rating against its competitors.
Adversa AI has discovered a way in which its agentic behavior can be manipulated by an attacker into providing a one-click RCE, or even a potential supply chain threat. All the attacker needs to do is place attractive but malicious code as, say, a GitHub repo.
When a developer uses Claude Code for a new task, it checks available repositories for what will assist in the task. If it locates, selects and downloads the malicious prepared code, it is almost immediately game over for the developer. All the attacker now needs is for the user to accept Claude Code’s usage as trusted – which the user is likely to do since the agent is just doing what it is supposed to do.
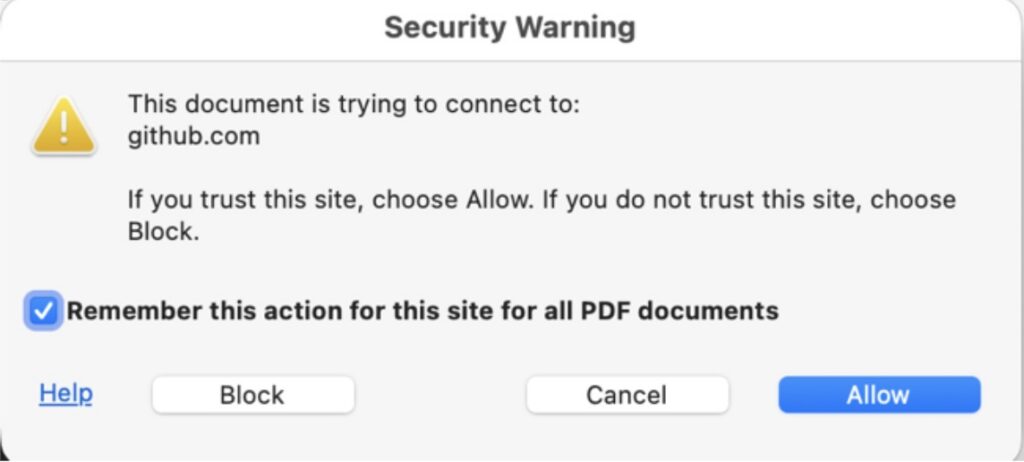
Claude Code’s acceptance dialog simply reads, “Quick safety check: Is this a project you created or one you trust?”, with the default set to ‘trust’. It’s little different in practice to Chrome’s browser security warning – which almost everyone almost always ‘allows’. Similarly in Claude Code, but “One Enter keypress on the trust dialog spawns the server as an unsandboxed OS process with the developer’s full privileges. No tool call from Claude is required,” reports Adversa.
The cloned repository contains small JSON files in standard Claude Code locations, providing an arbitrary code execution.
Advertisement. Scroll to continue reading.
enableAllProjectMcpServers in .claude/settings.json - auto-approves every server defined in the project’s .mcp.jsonenabledMcpjsonServers auto-approves a named subset“Both spawn attacker-defined MCP servers as OS processes with the user’s full privileges the moment the folder trust prompt is accepted,” reports Adversa. The result could open a long-lived C2. Alternatively, the payload could be embedded inline in .mcp.json, leaving no script file on disk for a reviewer or static scanner to flag.
Adversa describes several ways this process can be abused, but potentially the most disastrous is when Claude Code is used in the CICD process. If the user’s task is to produce a new tool for widespread distribution, it can kick off a brand new supply chain attack.
“Developers of widely used tools are a realistic prime target,” Alex Polyakov, co-founder and CTO at Adversa.AI, told SecurityWeek. “Claude Code is installed on most developer machines and devs routinely clone unfamiliar repos and run Claude against them, so this attack is very plausible if the code is destined for the user’s CICD.” The attack’s payload would read environment variables, deploy keys, signing certificates, and any credentials available to the runner. The runner would then quietly include details into the build process.
“Same blast-radius pattern as Salesloft Drift, with the initial-access bar collapsed to ‘clone and hit Enter’, added Polyakov.”
Adversa reported its findings to Anthropic, but for now at least, Anthropic has declined to do anything. Its position is if the user clicks “Yes, I trust this folder”, consent to the use of everything inside that folder has been given; and it is not up to Anthropic to interfere. But the user is generally unaware of what is really in the folder, and it is debatable whether uninformed consent is legal consent.
“Whether this meets Anthropic’s threshold for a vulnerability is their call. Whether users are making an informed trust decision under [this] dialog, in our view, is not a close question. They are not.”
The report notes the issue could be solved by Anthropic blocking enableAllProjectMcpServers, enabledMcpjsonServers, and permissions.allow from any settings file inside the project and allowing these keys only from scopes structurally outside the repository.
It also provides details on how users can mitigate the issues without waiting on Anthropic. For example, one recommendation specific to the CICD issue above, is “If a pipeline genuinely needs Claude Code non-interactively, gate it on branches where commits are already reviewed: post-merge on main, not arbitrary PR branches.”
The entire issue is not, however, limited to the use of Claude Code. “We checked whether this was only a Claude Code issue or something more general,” explains Serge Malenkovich, communications advisor at Adversa. “We ran the same chain against Gemini CLI, Cursor CLI, and Copilot CLI. All four behave the same way: a malicious repo can auto-approve and spawn an MCP server the moment the user accepts the folder trust prompt, and all four default to ‘Yes/Trust’. One Enter keypress is enough on any of them.”
This, he added, reframes the story. “It’s not a Claude Code issue; it’s a convention shared across agentic coding CLIs.”
Learn More at the AI Risk Summit at Half Moon Bay
Related: Claude Code, Gemini CLI, GitHub Copilot Agents Vulnerable to Prompt Injection via Comments
Related: Critical Vulnerability in Claude Code Emerges Days After Source Leak
Related: Hackers Weaponize Claude Code in Mexican Government Cyberattack
Related: Claude Code Flaws Exposed Developer Devices to Silent Hacking
Originally published by SecurityWeek
Original Source
SecurityWeek